Identity Theft in 2026: Real Phone and Bank Scam Stories
Identity theft in 2026 isn’t just something you read about in the news anymore—it’s happening to people we know. Recently, I heard several real-life stories from women in my own Gal Pal circle that truly stopped me in my tracks. These weren’t obvious scams or careless mistakes. They were sophisticated phone scams, bank fraud incidents, and even mobile account takeovers that could have happened to any of us. Real identity theft stories involving phone scams, bank fraud, and mobile account hacks. Learn how these scams happen and how to protect yourself in 2026.
What struck me most is how personal these situations felt. These weren’t strangers—they were friends, families, and people doing everything right. It was a powerful reminder that today’s digital scams are less about hacking computers and more about exploiting trust, urgency, and everyday technology we all use.
The more we understand how these scams work, the better prepared we are to protect our identities, our finances, and each other.
Friends, this is no longer something happening “out there.” It’s happening to people we know. And the best thing we can do is stay informed, stay vigilant, and look out for each other.
Key Takeaways
- Identity theft and scams stories are increasingly personal, affecting friends and family, not just strangers.
- Phone scams, SIM swap scams, and bank fraud incidents are on the rise, exploiting trust and urgency.
- Common tactics include phishing, data breaches, and social engineering to hijack identities.
- Protect yourself by securing your phone number, using authenticator apps, and monitoring dark web activity.
- Be vigilant and stay informed to prevent becoming a victim of these sophisticated scams.
The scary truth is that cyber attacks and phone scams are at a all time high:
- AI-enabled cyberattacks increased about 89% year-over-year in recent threat reports.
- Cybercrime is projected to cost the world about $10.5 trillion annually.
- Phishing and system intrusions remain the most common attack types.
Recent news suggest that attacks are becoming faster and more automated, with breaches sometimes spreading through networks in under 30 minutes.
These weren’t “too good to be true” emails or sketchy links. These were phone scams targeting families and women, designed to hijack trust, fear, and our instinct to protect the people we love.

The Verizon Text Scam That Shut Her Phone Down
The following is a shocking identity theft and scam my good friend Dana experienced. Dana received what looked like a legitimate text message from Verizon. The message asked if she was activating a new phone in-store.
She replied, “No.”
Within minutes, her phone went completely dark.
This was a SIM swap scam.
How SIM Swap Scams Work
In a SIM swap scam, criminals steal your phone number by convincing your mobile carrier to transfer it to a SIM card they control. Once your phone number is hijacked, you can no longer:
- Receive your calls and text messages
- Intercept two-factor authentication codes
- Reset your passwords
- Access banking, email, and social media accounts
When Dana’s phone number was stolen and then her digital identity was compromised, the highjackers had access to everything on her phone. Scary huh?
How a SIM swap scam works (simple explanation)
Step 1: They gather your information
Scammers first collect personal details about you:
• Email address
• Phone number
• Address
• Birthdate
• Answers to security questions
• Info leaked from data breaches or social media
Sometimes this comes from phishing texts or fake fraud calls.
Step 2: They contact your phone carrier
They call your mobile provider pretending to be you and say something like:
- “I lost my phone”
- “I got a new phone”
- “My SIM stopped working”
Then they ask the carrier to transfer your number to a new SIM card they control.
Step 3: Your phone suddenly stops working
This is the big warning sign.
Your phone may show:
• No service
• SOS mode
• No texts coming through
• Calls not working
Most people assume it’s just a network issue.
Meanwhile…
Step 4: They reset your passwords
Because many accounts send login codes via text, the scammer can now:
• Reset your email password
• Reset bank passwords
• Access Venmo/PayPal
• Take over Instagram
• Access crypto accounts
Your email is usually the main target because it unlocks everything else.
Step 5: They move fast
These scams usually happen very quickly:
• Password changes
• Money transfers
• Account lockouts
Sometimes within minutes to hours.
Biggest red flags 🚩
Tell your Gal Pals to watch for:
• Phone suddenly loses service for no reason
• Password reset emails you didn’t request
• Carrier alerts about account changes
• Bank alerts you didn’t initiate
• Locked out of email
Phone Scam & Mobile Carrier Identity Theft Statistics
How common phone-based identity theft is becoming
- About 22% of U.S. adults experienced account takeover fraud in one year (about 24 million households).
- Identity fraud overall has been increasing about 12% per year since 2020.
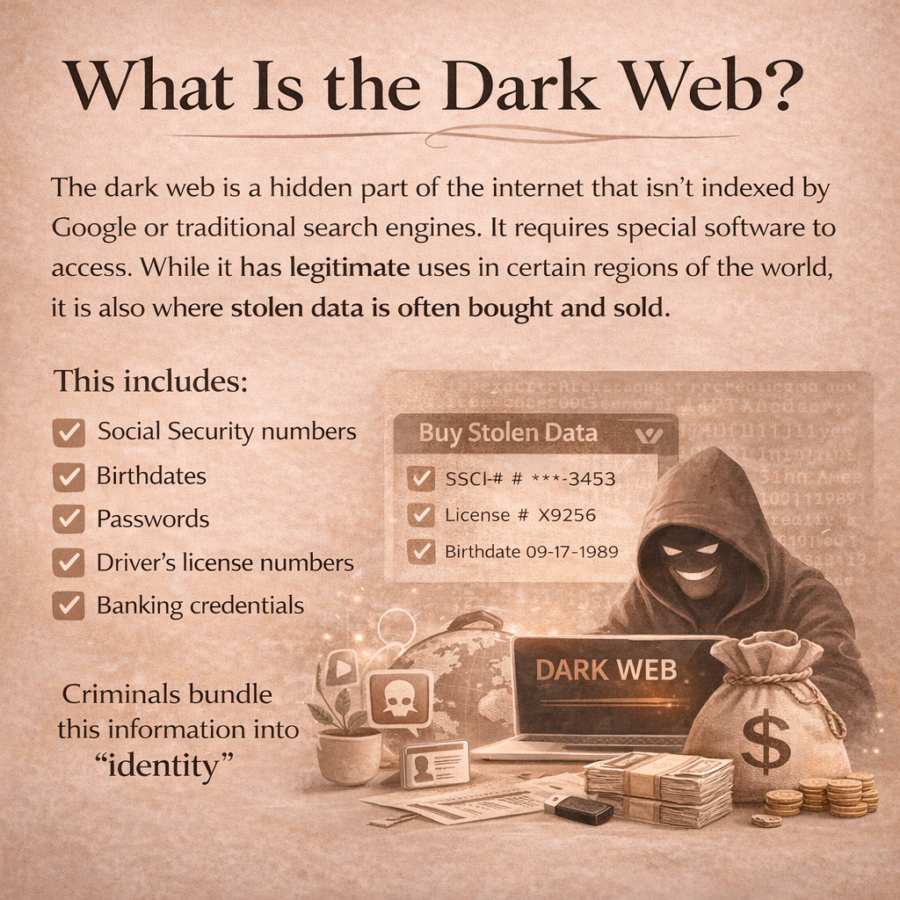
What Is the Dark Web?
After the SIM swap, Dana learned her personal information was circulating on what’s known as the dark web.
The dark web is a hidden part of the internet that isn’t indexed by Google or traditional search engines. It requires special software to access.
This includes the following personal identify:
- Social Security numbers
- Birthdates
- Passwords
- Driver’s license numbers
- Banking credentials
Criminals bundle this information into “identity packages” and sell it repeatedly. That means your information can circulate for years after the original breach.
How Criminals Gain Access to Your Identification
Many people assume identity theft happens because someone “clicked something.” That’s not always true.
Here are some of the most common ways criminals gain access to your ID:
Data Breaches
Retailers, medical offices, financial institutions, and apps are regularly hacked. Even if you’ve done nothing wrong, your data may have been exposed in a breach years ago.
Phishing Emails and Text Scams
Fake delivery notices, account alerts, or verification messages trick people into entering login credentials.
SIM Swap Scams
As Dana experienced, once criminals hijack your phone number, they can reset passwords and take over accounts.
Malware
Clicking an infected attachment or downloading unsafe software can install spyware that captures keystrokes and passwords.
Public Records and Social Engineering
Scammers piece together information from social media, online directories, and public records to impersonate you.
Password Reuse
Using the same password across multiple sites, one breach can unlock many accounts.
How Dana Is Protecting Her Identity Now
Since learning her personal identify is circulating on the dark web, Dana has taken significant steps to protect herself.
- She froze her credit with all three major credit bureaus
- She placed fraud alerts on her accounts
- She changed every password and now uses a password manager
- She switched from SMS verification to an authenticator app
- She added a port-out PIN with her mobile carrier
- She enrolled in dark web monitoring services- The Black Cloak which was recommended to her.
She describes the process as overwhelming—but ultimately empowering.
“I was at my bank yesterday to open yet another new debit card and my banker, Chris, told me he deals with three to four client fraud cases a week.” Dana
This is where Dana can share how it felt to realize her identity was compromised—and what she wants other women to know about acting quickly.
Mandi’s Story About A Debit Card Fraud Incident
One story that really opened my eyes came from my friend Mandi. Mandi’s husband was traveling for work when they received a fraud alert from their bank. His debit card had just been used at a Walmart in Florida—except there was one major problem…he wasn’t in Florida. In fact, the card had never even left his wallet.
Somehow, criminals had managed to clone his debit card information and use it hundreds of miles away while he still physically had the card in his possession.
If you’re wondering how that’s even possible, you’re not alone. This is exactly what makes modern cybercrime so unsettling.
How People Can Steal Your Debit Card Info
There are a few common ways criminals can steal card information without ever touching your physical card:
1. RFID or contactless card scanning (“digital pickpocketing”)
Many newer debit and credit cards have tap-to-pay technology. In rare cases, criminals with scanners can capture card data if they get very close (like in airports or crowded areas). While banks say the risk is low, it does happen.
2. Skimmers at gas stations or ATMs (most common)
This is the most likely scenario. If he previously used his card at a compromised gas pump, ATM, or payment terminal, a small hidden device (called a skimmer) could have copied the card data. Criminals then create a duplicate card and use it elsewhere.
3. Data breaches (very common now)
Sometimes the card information is stolen digitally from a retailer database breach or hacked payment processor. Criminals then sell the card numbers online where others use them to create physical clones.
4. Malware or phishing attacks
If card information was entered online or stored in an account that was compromised, criminals can obtain the numbers without ever seeing the card.
Why criminals often use Walmart or big retailers
Large retailers like Walmart are common fraud locations because:
- They can quickly test if a stolen card works
- Purchases can be resold easily
- Self-checkout makes transactions easier
- They can blend in with normal shoppers
The Phone Call That Made My Heart Stop- Family Emergency Scam
On a Sunday afternoon I noticed I kept getting calls from a number I didn’t recognize. Eventually, I answered.
On the other end, I heard crying and chaos.
“Mom, I am so sorry! I was in an accident.” The voice didn’t sound like my son but my heart stopped nevertheless.
Then a man came on the line and said, “Your daughter is safe with us.”
“I don’t have a daughter, you have the wrong number!” Without hesitation, they pivoted.
“It’s your sister”, they told me.
I hung up immediately and called my sister and son’s girlfriend. Everyone was safe. Then I reported the call to police.
This is known as a family emergency scam or “crying phone call scam.” Criminals rely on fear and urgency to get money before you can verify the situation.
What this scam usually looks like:
A parent gets a call where:
- Someone pretends to be their child (sometimes using AI voice cloning)
- Or someone claims to be a police officer, doctor, or lawyer
- They say the child was in an accident or arrested
- They create panic and urgency
- They ask for money quickly (wire, Zelle, gift cards, bail money)
This is criminal fraud and attempted financial exploitation.
Why this is happening more now (2026 trend)
Criminals can now:
- Pull names from social media
- Find family relationships online
- Clone voices from short videos
- Spoof phone numbers to look local
This is why the scam feels so real.
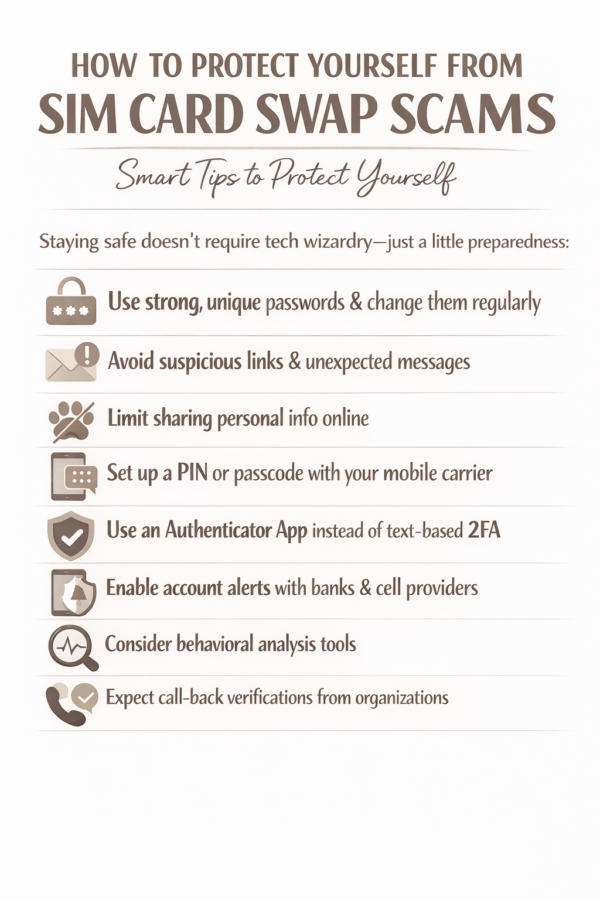
How to Protect Your Phone Number From Scams
Your phone number is now the key to your digital life. Protect it like you would your Social Security number.
- Don’t reply to unexpected carrier texts
- Call companies directly using official website numbers
- Add a port-out PIN with your mobile provider
- Use authenticator apps instead of SMS codes
- Freeze your credit (it’s free and reversible)
- Verify emergency calls before sending money
If you believe your phone number has been hijacked, contact your carrier immediately and secure your email first.
Time matters.
FAQ- Frequently Asked Questions
What is a SIM swap scam?
A SIM swap scam is when criminals trick your mobile carrier into transferring your phone number to a SIM card they control. This allows them to intercept calls, text messages, and authentication codes to access your accounts.
What is the dark web?
The dark web is a hidden portion of the internet that requires special software to access. It is often used to buy and sell stolen personal data, including Social Security numbers and login credentials.
How do criminals steal your phone number?
Criminals use social engineering, stolen personal information from data breaches, and phishing scams to convince mobile carriers to transfer a phone number to a new SIM card.
What should I do if my phone number is hijacked?
Contact your carrier immediately, secure your email accounts, freeze your credit, change passwords, and place fraud alerts on your accounts.